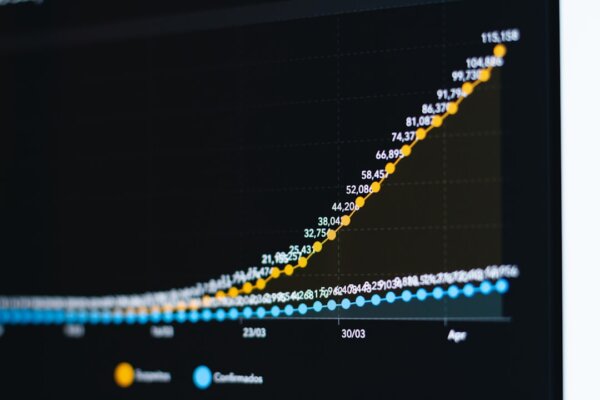
Photo by Sasun Bughdaryan on Unsplash
Decoding the Anomaly: When Trust Collides
In the world of cybersecurity, digital certificates issued by Certificate Authorities (CAs) like DigiCert are the bedrock of trust. They verify identities, encrypt communications, and ensure that the software you download is legitimate and untampered. So, when a leading security solution like Microsoft Defender starts flagging certificates issued by a reputable CA like DigiCert, it immediately raises concerns and sends ripples through IT departments worldwide.
This isn’t necessarily an indication that DigiCert itself is compromised, nor does it automatically mean your systems are under attack. Instead, it’s a call to action – an alert that requires careful investigation. Understanding why Defender might issue such an alert is crucial for maintaining your organization’s security posture and ensuring the integrity of your digital assets.
Why Would Defender Flag a DigiCert Certificate? Exploring the Possibilities
The complexity of modern IT environments means there isn’t a single, straightforward answer to why Microsoft Defender might flag a certificate from DigiCert. Here are several common scenarios:
- Expired or Revoked Certificates: The most obvious reason is that the certificate in question has either expired or been revoked by DigiCert. Defender checks the validity period and against Certificate Revocation Lists (CRLs) or Online Certificate Status Protocol (OCSP) responders. If a certificate is no longer valid, Defender will rightly flag it, regardless of its original issuer.
- Misconfigured Certificate Trust Settings: Your system’s trust store or PKI (Public Key Infrastructure) configuration might be outdated or incorrect. If your system hasn’t updated its root certificate authorities or CRLs, it might incorrectly deem a valid DigiCert certificate as untrusted or suspicious.
- Suspicious Usage of Valid Certificates: Sometimes, malware or unwanted applications are signed with legitimate certificates – either because the certificate was stolen, or the signer is intentionally malicious but obtained a valid certificate through deceptive means. In such cases, Defender might not be flagging the certificate’s validity but rather the *behavior* of the executable or process it signs, which is deemed suspicious.
- Certificate Pinning Issues: Some applications implement certificate pinning, expecting a very specific certificate for certain connections. If a different, albeit valid, DigiCert certificate is presented (perhaps due to an updated certificate or an intermediary proxy), it could trigger an alert within the application and subsequently, Defender.
- Heuristic Detections or False Positives: Security software, including Defender, uses heuristic analysis to detect new and evolving threats. These algorithms can sometimes produce false positives, flagging legitimate files or processes based on patterns that mimic malicious activity. An aggressive heuristic might flag a legitimate DigiCert-signed component due to certain behavioral characteristics.
- Intermediate Certificate Issues: Trust chains are critical. If an intermediate certificate in the chain is missing or untrusted on the client machine, even a perfectly valid end-entity certificate from DigiCert will fail to validate, leading to alerts.
Your Action Plan: Investigating and Resolving DigiCert Alerts
When you encounter a Microsoft Defender alert related to a DigiCert certificate, a methodical approach is key:
- Don’t Panic, Investigate the Alert Details: Go to the Defender Security Center and examine the full details of the alert. What is the file path? The process name? The specific certificate details (serial number, thumbprint, issuer, subject)? This information is vital for diagnosis.
- Verify Certificate Status: Use system tools like
certutil -verify -urlfetch [path_to_certificate_file]or an online certificate checker to confirm the certificate’s validity, expiration date, and revocation status directly from DigiCert’s sources. - Examine Associated Files and Processes: Is the flagged certificate associated with a known, legitimate application? Or is it tied to an unfamiliar process or file location? If it’s a system file, check its integrity. If it’s a third-party application, verify its authenticity.
- Update Microsoft Defender and Your OS: Ensure your Microsoft Defender definitions are fully up-to-date. Also, confirm your operating system and applications have the latest security patches, as these often include updated root certificates and PKI components.
- Review PKI Infrastructure: For enterprise environments, ensure your internal PKI infrastructure (if applicable) is correctly configured to trust DigiCert’s root and intermediate CAs, and that CRLs are being retrieved successfully.
- Report False Positives: If, after thorough investigation, you are confident that the alert is a false positive and the certificate and associated process are legitimate, consider submitting the file or certificate to Microsoft for analysis. This helps improve Defender’s detection accuracy.
Conclusion: Vigilance in a Complex Digital World
Microsoft Defender flagging DigiCert certificates is a situation that demands your attention, but not necessarily panic. It underscores the complexity of modern cybersecurity and the intricate dance between trust authorities, security tools, and the myriad applications running on our systems. By systematically investigating the root cause, you can differentiate between a legitimate security threat, a simple misconfiguration, or a false positive.
Maintaining a proactive stance, regularly updating your security software, diligently managing your certificates, and understanding your system’s trust configurations are paramount. Stay vigilant, stay informed, and ensure your digital environment remains secure.